Protecting your customers’ payment data has never been more important. With increasing threats of fraud and data breaches, businesses need to ensure that their payment systems are secure, compliant and protected against tampering. That’s where PED P2PE Asset Management from MCR Systems comes in.
What is PED P2PE?
PED (PIN Entry Device) P2PE (Point-to-Point Encryption) is a security standard that encrypts payment card data from the moment it’s entered the device until it reaches the secure payment processor. This prevents sensitive cardholder information from being exposed or intercepted during the transaction process.
Under the Payment Card Industry Data Security Standard (PCI DSS), businesses must carry out tamper checks on their PEDs weekly or perform a risk assessment to determine a suitable inspection frequency. This can be complex and time-consuming – but with MCR Systems, you don’t have to manage it alone.
How MCR Systems supports you
Our PED P2PE Asset Management service takes responsibility for managing and securing your PEDs, helping to protect your customers’ card data and keeping you compliant with PCI DSS requirements.
Here’s what we do:
Making tamper checks simple
To streamline weekly tamper checks, we tailor a custom pop-up notification on your POS system. You control its frequency (daily, weekly, monthly), the time it appears and whether it can be deferred – with full tracking of deferrals.
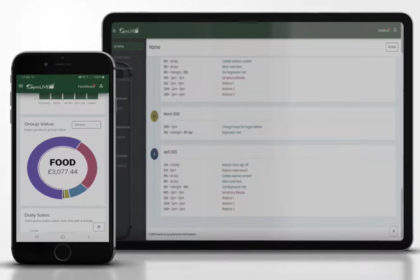
When the notification appears, a manager or supervisor quickly checks the PED for damage or interference and confirms that its serial number matches what the system expects. The whole process takes less than 60 seconds per terminal, and every check is securely logged and accessible through our Symphony Suite reporting feature.
Why it matters
In a world where fraud and data breaches continue to pose significant risks, PED P2PE Asset Management provides a proactive layer of protection. It safeguards your customers’ payment card data, supports compliance with PCI DSS and gives your business peace of mind that your systems are secure.
Protect your business and your customers with MCR Systems’ PED P2PE Asset Management.
Call us on 0116 299 7000 or email enquiries@mcr-systems.co.uk